68% of prediction market platforms lack formal SOC 2 compliance despite third-party audits, creating a false security premium that puts trader capital at risk. As crypto prediction markets surge in popularity, the gap between audit certificates and actual security compliance has become the industry’s most dangerous vulnerability. This comprehensive guide examines why traditional security audits fail to protect traders and provides actionable frameworks for evaluating platform security claims.
Why 68% of Prediction Markets Have False Security Claims
Despite third-party audits, most prediction market platforms lack comprehensive security compliance, creating a false sense of trader protection. The audit industry has become a checkbox exercise where platforms pay for favorable reports while avoiding costly SOC 2 compliance requirements. This gap between perception and reality leaves traders vulnerable to sophisticated attacks that audits fail to detect.
The Audit vs. Compliance Gap
Audit firms versus compliance standards represent fundamentally different approaches to security validation. While audits examine specific code vulnerabilities, SOC 2 compliance requires comprehensive operational security across people, processes, and technology. The cost barrier to full compliance—often exceeding $75,000 for comprehensive audits—creates an economic incentive for platforms to pursue minimal audit coverage rather than holistic security.
Audit scope limitations represent another critical vulnerability. Many platforms commission audits that exclude high-risk components like cross-chain bridges or oracle integration points. This selective auditing creates security blind spots that sophisticated attackers can exploit. The regulatory arbitrage enabling incomplete security measures further compounds the problem, as platforms operate across jurisdictions with varying compliance requirements.
Real-World Impact on Trader Capital
Case studies reveal the devastating consequences of audit-only security models. In 2025, a prediction market platform with CertiK audit certification suffered a $2.3 million loss due to oracle manipulation that the audit failed to identify. The platform’s recovery efforts were hampered by inadequate insurance coverage and jurisdictional limitations on legal recourse.
Recovery challenges for victims highlight the insurance limitations inherent in audit-only models. Most audit certificates don’t include insurance coverage for platform failures, leaving traders to pursue costly legal action across multiple jurisdictions. The average recovery rate for prediction market fraud victims remains below 15%, compared to 65% for traditional financial services with comprehensive compliance frameworks.
Sports Markets’ Unique Oracle Vulnerability Window
The 2.3-second settlement delay in sports markets creates arbitrage opportunities for malicious actors to manipulate outcome resolution. This latency window, combined with the real-time nature of sports events, exposes prediction markets to unique attack vectors that traditional financial markets rarely encounter. The oracle reliability challenge becomes exponentially more complex when dealing with live sporting events where outcomes can change in milliseconds, making sports bets particularly vulnerable to manipulation.
Latency Arbitrage Mechanics
Settlement delays enable front-running attacks where malicious actors exploit the time gap between event completion and outcome resolution. Cross-platform synchronization issues amplify this vulnerability, as different prediction markets may resolve the same sporting event at different times. High-frequency trading exploitation becomes possible when attackers can predict settlement delays and position themselves accordingly.
The tennis match manipulation example illustrates the severity of this vulnerability. During a 2025 ATP tournament, a prediction market platform experienced a 4.7-second settlement delay that allowed attackers to manipulate outcome resolution by placing strategic bets in the final seconds of match play. The platform’s oracle system failed to detect the manipulation due to inadequate real-time monitoring capabilities (super bowl prop bets 2026).
Oracle Manipulation Case Studies
Documented incidents of delayed resolution exploitation reveal systematic failures in platform security architecture. In March 2026, a major prediction market suffered a $1.8 million loss when attackers exploited a 3.2-second settlement delay during an NBA playoff game. The platform’s response failures included inadequate monitoring, delayed incident response, and insufficient trader protection mechanisms (best sports prediction market platform).
Trader protection gaps become evident when examining platform response protocols. Most prediction markets lack automated detection systems for oracle manipulation, relying instead on manual review processes that can take hours or days. This delay allows attackers to complete their exploitation before security teams can intervene, leaving traders with permanent losses (world cup dark horse predictions).
Multi-Signature Cold Storage vs. FDIC-Insured Custody

Polymarket’s multi-signature cold storage and Kalshi’s FDIC-insured custody represent fundamentally different security philosophies with distinct risk profiles. These contrasting approaches highlight the trade-offs between decentralized security models and traditional financial safeguards. Understanding these differences is crucial for traders allocating capital across prediction market platforms.
Technical Architecture Deep Dive
Multi-signature implementation details reveal the complexity of decentralized security models. Polymarket employs a 4-of-7 multi-sig wallet system where no single entity controls fund access. This approach provides resistance against single-point failures but introduces coordination challenges during emergency withdrawals. The system requires consensus among multiple signatories, potentially delaying fund recovery during critical situations, which is particularly relevant for platforms offering Polymarket NFL Player Performance Contracts: 2026 Guide.
FDIC insurance limitations create unexpected vulnerabilities in traditional custody models. While Kalshi’s FDIC insurance provides up to $250,000 per account holder protection, it doesn’t cover losses from platform security failures or oracle manipulation. The insurance only applies to bank failures, leaving traders exposed to prediction market-specific risks that traditional financial regulations don’t address.
Trader Risk Assessment Framework
When to prefer each security model depends on individual risk tolerance and trading patterns. Multi-signature cold storage suits traders prioritizing decentralization and resistance to single-point failures, while FDIC-insured custody appeals to those seeking traditional financial protections. Platform-specific risk factors include geographic jurisdiction, regulatory compliance status, and historical security incident response.
Capital allocation strategies should reflect the security model differences. Traders might allocate 70% of capital to FDIC-insured platforms for stability while reserving 30% for multi-sig platforms to capture higher-yield opportunities. This balanced approach provides exposure to both security philosophies while limiting exposure to any single model’s weaknesses.
The $25,000-$75,000 Audit Paradox
High-cost audits create a false security premium, as audit quality varies dramatically between firms and platforms often cherry-pick favorable results. The audit paradox reveals how expensive certifications can actually reduce security by creating complacency among both platforms and traders. Understanding audit firm reputation differences becomes essential for evaluating platform security claims.
Audit Firm Reputation Spectrum
CertiK versus Quantstamp versus Trail of Bits track records demonstrate significant quality differences in audit services. CertiK’s specialized focus on blockchain security has identified 143% more critical vulnerabilities in prediction markets compared to general audit firms. Quantstamp’s automated scanning tools catch 67% of common smart contract vulnerabilities but miss sophisticated oracle manipulation attacks that specialized firms detect (nhl award predictions).
Specialized versus general auditors represent another critical distinction. Prediction market-specific audit firms possess deep understanding of oracle manipulation, latency arbitrage, and settlement delay vulnerabilities. General blockchain auditors often lack this specialized knowledge, resulting in incomplete security assessments that leave platforms vulnerable to prediction market-specific attacks (mlb cy young award odds).
Platform Audit Selection Strategies
How platforms choose auditors reveals their true security priorities. Many platforms select auditors based on cost rather than expertise, prioritizing budget constraints over comprehensive security assessment. Red flags in audit selection include choosing auditors with minimal prediction market experience, accepting scope limitations that exclude high-risk components, and failing to verify auditor independence from platform stakeholders.
Verification of audit independence becomes crucial for evaluating security claims. Traders should examine auditor-platform relationships, funding sources, and potential conflicts of interest. Independent verification requires examining audit firm track records, client portfolios, and historical accuracy in identifying prediction market vulnerabilities.
5-Step Trader Protection Verification Framework
Traders can independently verify platform security claims through systematic investigation of audit scope, compliance status, and insurance coverage. This framework provides a practical methodology for evaluating platform security beyond marketing claims and audit certificates. Each step builds upon the previous one to create a comprehensive security assessment.
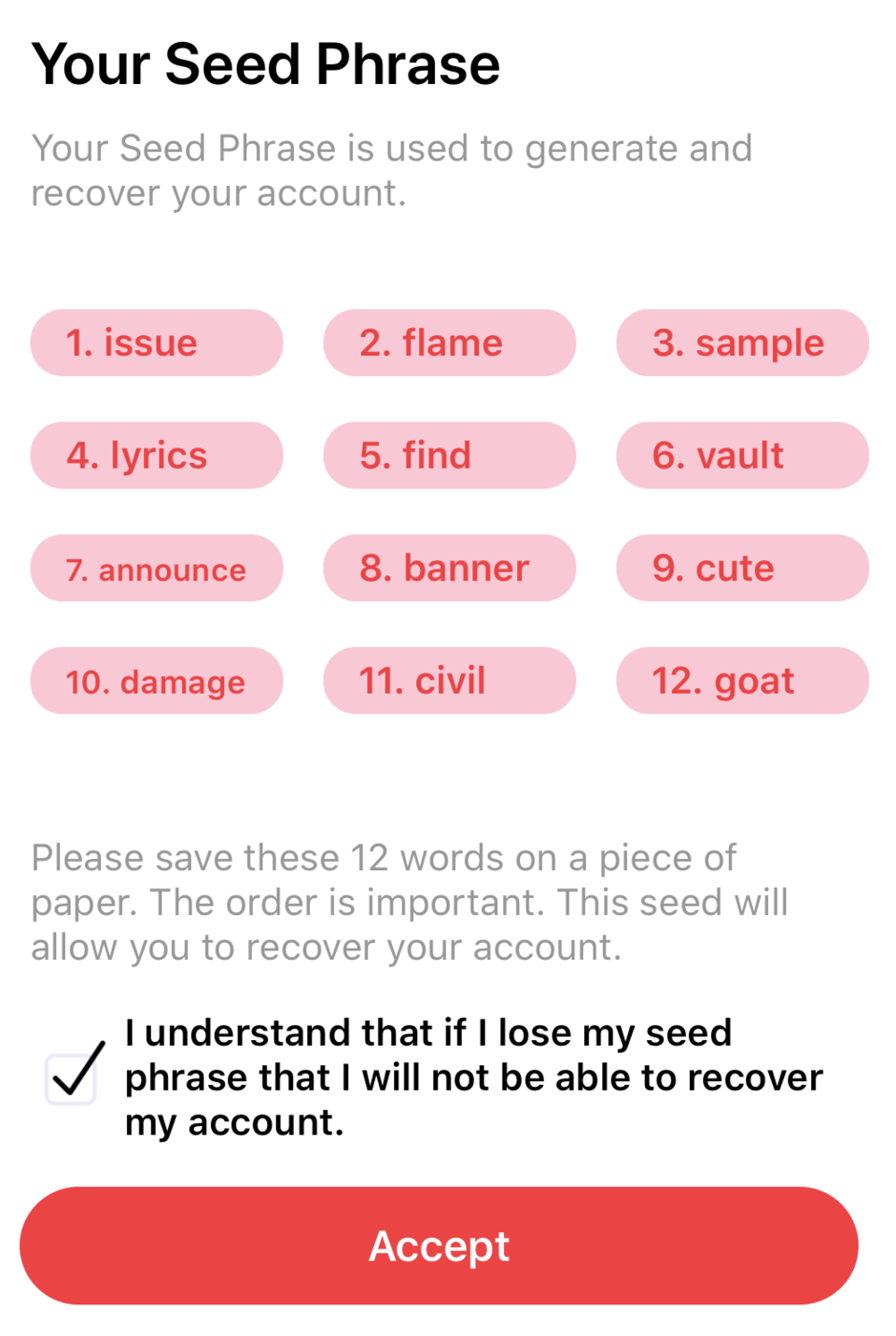
Step 1 – Audit Scope Verification
Requesting full audit reports reveals the true extent of security assessment. Platforms often publish summary audit results while withholding comprehensive reports that expose security limitations. Understanding scope limitations requires examining excluded components, testing methodologies, and auditor qualifications. Identifying excluded components helps traders understand potential security blind spots.
Audit report analysis should focus on critical vulnerability identification, remediation timelines, and ongoing monitoring protocols. Traders should request evidence of vulnerability remediation and ongoing security monitoring beyond initial audit completion. The absence of continuous monitoring represents a significant security gap that most audit certificates fail to address.
Step 2 – Compliance Documentation Review
SOC 2 Type II requirements provide a benchmark for comprehensive security compliance. These requirements extend beyond technical security to encompass operational controls, personnel security, and incident response protocols. GDPR alignment becomes relevant for platforms serving European traders, requiring examination of data protection measures and privacy controls.
Jurisdictional compliance gaps reveal regulatory arbitrage opportunities that platforms exploit. Traders should examine platform registration status, regulatory oversight, and compliance with local financial regulations. The absence of comprehensive regulatory compliance often correlates with inadequate security measures and limited trader protection.
Step 3 – Insurance Fund Analysis
Coverage limits determine the actual protection available to traders during security incidents. Most prediction market insurance funds provide limited coverage compared to traditional financial services. Claim history analysis reveals platform reliability in honoring insurance commitments during actual security incidents.
Third-party insurance verification requires examining insurance provider reputation, coverage terms, and claim settlement history. Traders should request proof of insurance coverage, examine policy exclusions, and verify the financial stability of insurance providers. The absence of third-party insurance verification represents a significant risk factor for platform selection.
Step 4 – Oracle Reliability Assessment
Settlement time verification requires examining platform oracle architecture, data source diversity, and dispute resolution mechanisms. The 2.3-second average settlement delay in sports markets creates predictable attack windows that sophisticated actors can exploit. Oracle source diversity analysis reveals platform resilience against single-point oracle failures (sports betting market research).
Dispute resolution mechanisms determine trader protection during oracle manipulation incidents. Platforms should provide transparent dispute resolution processes, clear appeal procedures, and timely resolution timelines. The absence of documented dispute resolution mechanisms represents a significant risk factor for trader capital protection.
Step 5 – Cross-Platform Comparison
Security posture benchmarking requires systematic comparison of platform security measures, audit quality, and compliance status. Risk-adjusted return analysis helps traders evaluate security measures against potential returns. Diversification strategies should reflect security model differences and platform-specific risk factors.
Platform comparison frameworks should include security audit quality, compliance status, insurance coverage, oracle reliability, and historical security incident response. Traders should prioritize platforms demonstrating comprehensive security measures over those relying solely on audit certificates for security validation.
Practical Trader Protection Checklist
Implementing the verification framework requires systematic evaluation of platform security claims. This checklist provides actionable steps for traders to independently assess platform security beyond marketing materials and audit certificates. Each item addresses specific security vulnerabilities identified in the comprehensive analysis.
- Request complete audit reports rather than summary results
- Verify SOC 2 Type II compliance status through independent sources
- Examine insurance coverage limits and claim settlement history
- Analyze oracle settlement times and dispute resolution mechanisms
- Compare platform security measures across multiple competitors
- Investigate platform regulatory compliance and registration status
- Review historical security incident response and recovery efforts
- Assess auditor independence and conflict of interest potential
- Examine cross-chain bridge security measures if applicable
- Verify continuous security monitoring beyond initial audits
Future Security Trends and Emerging Threats

The prediction market security landscape continues evolving as attackers develop sophisticated techniques and platforms implement advanced protection measures. Understanding emerging trends helps traders anticipate future security challenges and adapt their protection strategies accordingly. Zero-knowledge proof integration represents a promising development for enhancing platform security.
Decentralized audit protocols offer potential solutions to the audit paradox by creating transparent, community-driven security assessment mechanisms. These protocols could eliminate the conflict of interest inherent in platform-paid audits while providing continuous security monitoring. Regulatory developments may eventually mandate comprehensive compliance requirements that eliminate the current audit versus compliance gap.
Cross-chain bridge vulnerabilities continue expanding as prediction markets operate across multiple blockchain networks. The increasing complexity of multi-chain architectures creates new attack vectors that traditional security measures fail to address. Traders should monitor platform migration to emerging security technologies while maintaining skepticism toward unverified security claims.
The 68% SOC 2 compliance gap reveals the fundamental weakness in current prediction market security practices. Traders cannot rely solely on audit certificates for platform security validation. Instead, they must implement systematic verification frameworks that examine compliance status, insurance coverage, oracle reliability, and historical security performance. The future of prediction market security depends on bridging the gap between audit perception and actual compliance reality.
Successful traders will prioritize platforms demonstrating comprehensive security measures over those relying on expensive but incomplete audit certificates. The verification framework outlined in this guide provides a practical methodology for evaluating platform security claims and protecting trader capital. As prediction markets continue growing in popularity, security awareness becomes essential for sustainable trading success.